Plunge deep into the mysterious world of onion links. These layered pathways lead users through various series of encryption, guarding their true destination. Navigate these virtual tunnels with caution, as they may encounter challenges along the way.
- Comprehending the structure of onion links is crucial for successfully utilize them.
- Tools exist exclusively designed for interacting with these unique links.
- Ethical practices are essential when engaging with the world of onion links, as it can contain both risks.
Unveiling the Mysteries of Onion Links
Onion links have become a popular tool in the world of cybersecurity. These complex links encrypt their true destination, making them difficult to trace. Analysts are constantly striving to decipher the mysteriesbehind onion links, aiming to mitigate their abuse.
- It's often argued that onion links provide a crucial avenue for whistleblowers to operate anonymously.
- However, they can also be used by malicious actors for dark purposes.
The future of onion links remain an open question. As technology evolves, the challenge to maintain user protection will continue to .
Navigating the Darknet: A Guide to Onion Links
The darknet, a shadowy realm of encrypted networks, holds both mysteries and risks. Accessing this hidden world necessitates special tools, primarily onion links. These unique URLs, constructed with the .onion identifier, act as gateways to websites operating on the Tor network, providing concealment. Unlocking these hidden sites can be a daunting task, requiring knowledge of specific methods.
- To begin with, you'll need to install the Tor browser. This specialized application obscures your internet traffic, shielding your identity and location from prying eyes.
- Secondly, locate a reputable source for onion links. Be wary of frauds and untrusted sources, as they may lead to malicious websites or security breaches.
- Finally, once you've discovered a valid onion link, simply enter it into the Tor browser's address bar and press Enter. This will transfer you to the hidden website.
Always be aware that navigating the darknet carries inherent risks. Exercise extreme vigilance, and never reveal sensitive information unless you are absolutely certain of the website's legitimacy.
Anonymous Connections: A Guide to Secure Browsing
The deep web can be a daunting place, offering both privacy and risk. To prudently navigate this virtual landscape, understanding the necessity of onion link security is vital.
- Employ robust encryption to protect your data
- Reduce the use of personal information while browsing
- Evaluate websites before engaging
Exploring Hidden Worlds: The Power of Onion Links
In the vast expanse within the digital realm, obscure worlds often exist dormant. These enigmatic spheres offer tantalizing glimpses into alternate dimensions, waiting to be penetrated. Onion links serve as gateways to these enigmatic realms. By clicking on seemingly ordinary links, users embark on a quest that unveils truths of hidden knowledge, coded messages, and unexpected discoveries.
- Deciphering the pattern within onion links demands a discerning eye.
- Each activation can unveil a different layer, directing the explorer deeper into the heart of the hidden world.
Embrace the thrill of exploring these cybernetic mazes. The route is often surprising, but the rewards can be enormous
The Anatomy of an Onion Link
Navigating the darknet can feel like embarking into a labyrinthine puzzle. At its heart, the foundation lies in understanding onion links, obscure addresses that lead to hidden online destinations. These links, disguised as seemingly random strings of characters, utilize a sophisticated onionlinks encryption protocol known as the Onion Router, or TOR.
- Analyzing the layers of an onion link reveals its elaborate structure. Each layer acts as a separate server, scrambling the data flowing between users and the final destination.
- Those layers create a barrier that hides the true origin of both the user and the server, boosting anonymity and protection.
Completely understand how onion links work, one must investigate into the mathematics behind TOR. By breaking down this code, we can unlock the secrets hidden within these enigmatic digital pathways.
 Hallie Eisenberg Then & Now!
Hallie Eisenberg Then & Now! Jennifer Love Hewitt Then & Now!
Jennifer Love Hewitt Then & Now!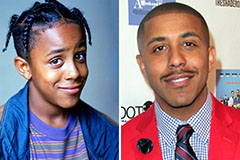 Marques Houston Then & Now!
Marques Houston Then & Now! Kelly Le Brock Then & Now!
Kelly Le Brock Then & Now! Raquel Welch Then & Now!
Raquel Welch Then & Now!